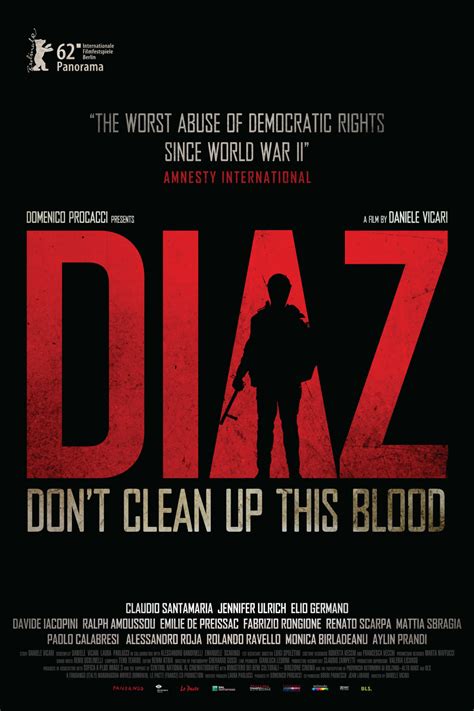
Diaz: Don’t Clean Up This Blood. A Film on the Memory of Violence at the G8 Summit in Genoa
The film “Diaz: Don’t Clean Up This Blood” (2012), directed by Daniele Vicari, reconstructs a key episode in recent European political memory: the police repression during the G8 summit in Genoa. It is a work focused on institutional violence and the cover-up of events that took place at the Armando Diaz School. The historical context is set in July 2001, during the G8 counter-summit in Genoa, when thousands of people mobilized against the global neoliberal model. The raid on the … Read more